At Atlassian Team26, the Compliance Alliance hosted the 5th Compliance Workshop on May 7th that focused on one of the biggest questions facing regulated industries today:
How can organizations adopt AI on Atlassian Cloud without compromising security, governance, compliance, or trust?
The workshop brought together Atlassian Marketplace Partners and Solution Partners working with highly regulated organizations on Jira and Confluence Cloud.
One of the highlights was a deep dive into Atlassian Rovo, presented by Ashwini Rattihalli, Principal Product Manager for Rovo at Atlassian.
Her session explored how Atlassian is approaching enterprise AI adoption for industries where governance requirements are not optional, but foundational.
Rovo in Regulated Industries: Key Takeaways
A quote from Ashwini’s presentation captured the atmosphere in many regulated organizations perfectly:
“If we do not adopt AI as a fundamental way to get work done, we will literally go out of business. But on the other hand, AI is incredibly dangerous, and we need to be thoughtful before we deploy it.”
Organizations want the productivity gains AI promises, but they also need transparency, controls, auditability, and predictable data handling before enabling AI at scale.
Rather than positioning Rovo as a separate AI layer bolted onto Atlassian products, the session emphasized that Rovo is built directly into the Atlassian platform and inherits existing enterprise controls.
For customers already operating Jira and Confluence in regulated environments, this matters. It means AI adoption does not necessarily require starting security and compliance reviews from scratch.
Security and Compliance Foundations Already in Place
Ashwini outlined the security baseline currently available for Rovo, including SOC 2 and ISO 27001 compliance, customer-managed encryption keys, IP allowlisting, and data residency support.
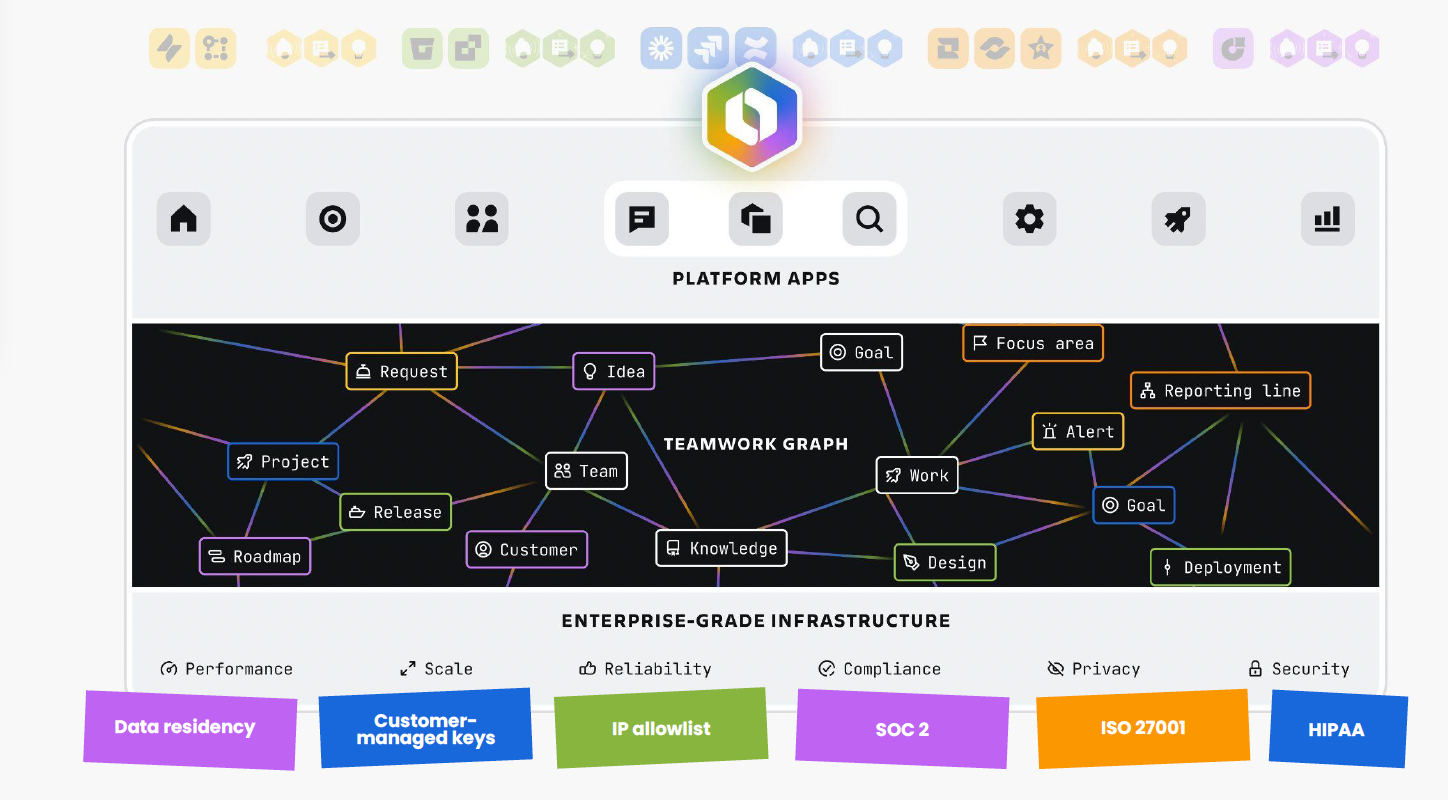
Customer-managed keys were highlighted as a major milestone launched recently, giving organizations more control over encryption and access management. Ashwini also confirmed ongoing work toward ISO 42001 certification, although timelines remain dependent on lengthy audit and certification processes.
Another important discussion point was European compliance requirements. Ashwini indicated ongoing work to ensure Rovo aligns with evolving EU expectations and regulatory obligations, particularly around AI governance and data handling outlined in the EU AI Act.
For many attendees, however, the biggest concern was not certifications alone, but how AI models actually process customer data.
How Rovo Handles Data and LLM Interactions
A significant portion of the conversation focused on what happens behind the scenes when users interact with Rovo.
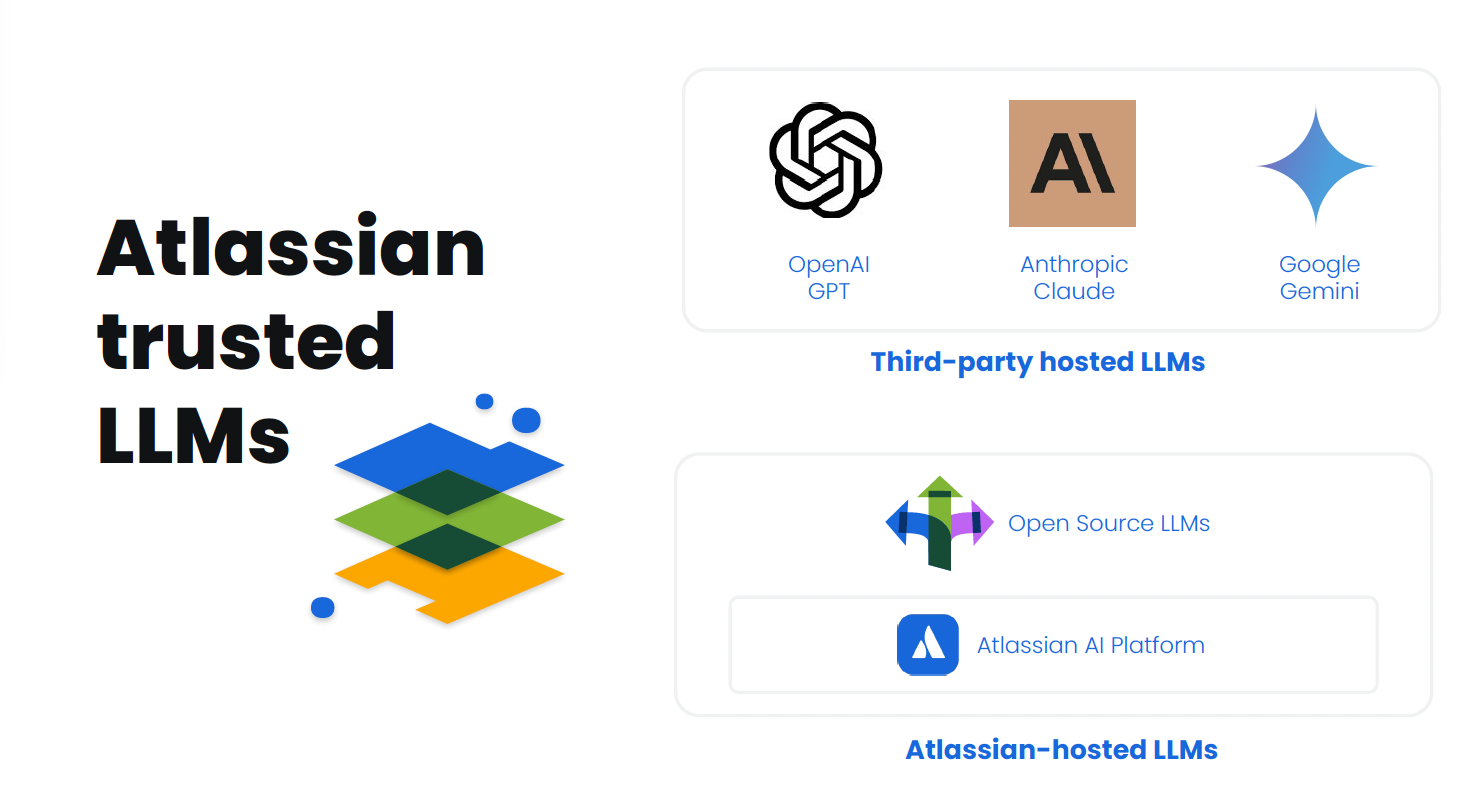
Ashwini explained that Rovo uses a combination of third-party hosted LLMs, such as OpenAI and Google Gemini, alongside Atlassian-hosted open-source models including Llama and Gemma.
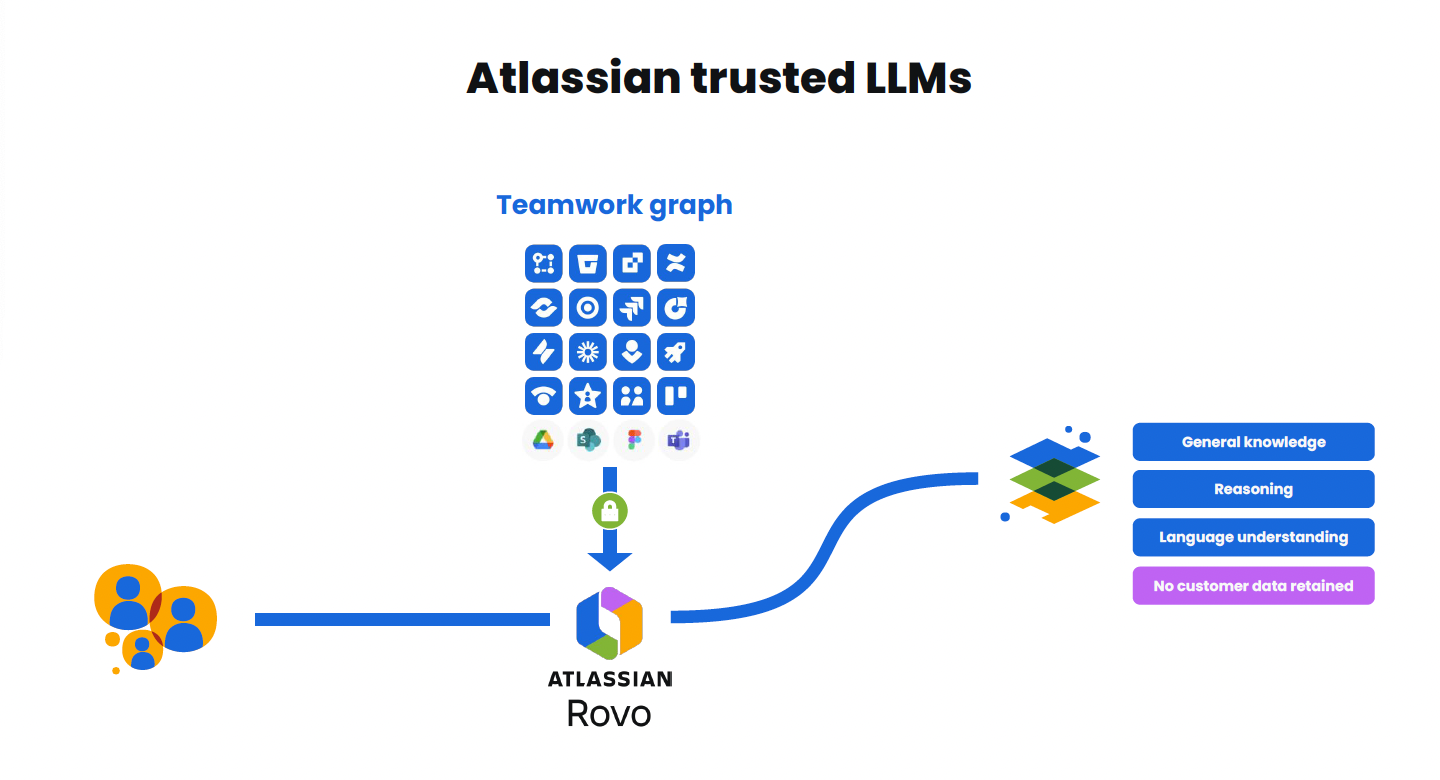
The architectural distinction is important for organizations with stricter governance requirements who may choose to rely only on Atlassian-hosted models to keep data routing tighter, even if that comes with some functional trade-offs.
The session repeatedly emphasized that prompts and responses sent to third-party LLM providers are not retained and are not used to train external models. According to Ashwini, contextual data assembly happens within Atlassian boundaries before only the relevant request context is sent to the model.
The retrieval process itself was also discussed in detail – Rovo first interprets the user’s query, retrieves relevant information from the Teamwork Graph and connected systems, and then sends only bounded contextual information to the model before generating a response.
Permissions remain enforced throughout the process so users only receive information they are already authorized to access in the first place.
For attendees from regulated sectors, this permission-aware retrieval model was one of the most reassuring parts of the discussion.
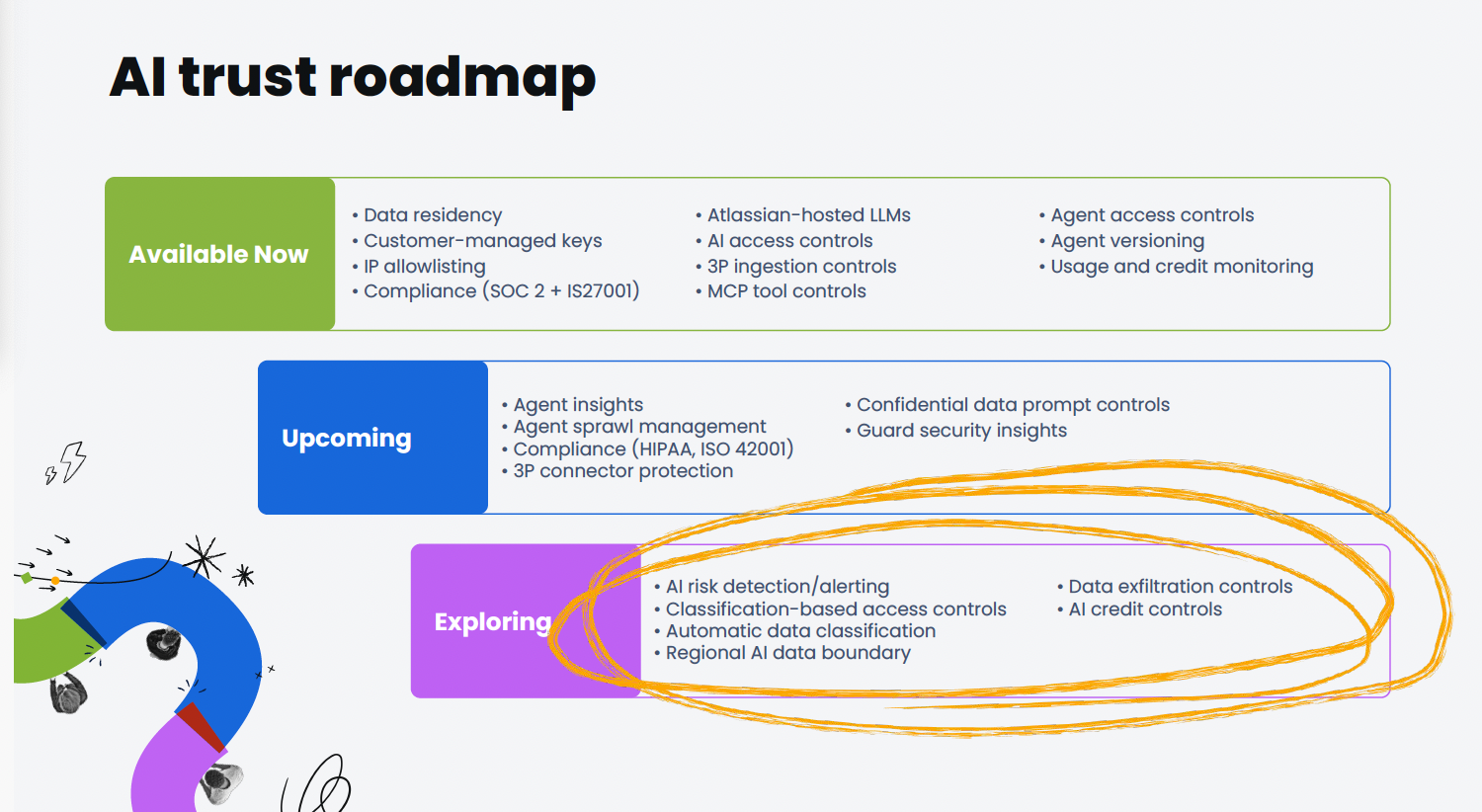
Regional AI Boundaries Are Becoming a Major Requirement
While Atlassian already supports data residency at rest, many customers are now asking for something more specific: regional AI processing boundaries.
Organizations want guarantees not just about where data is stored, but where AI inference and processing occur. Ashwini acknowledged this demand and shared that regional AI processing is currently being explored, beginning with the EU.
The challenge, however, is not entirely within Atlassian’s control. Availability depends heavily on regional support from hyperscalers and third-party model providers. Regions such as Australia, Singapore, and India currently lag behind in local model availability.
Still, the message from the audience was clear: regional AI controls are rapidly moving from “nice to have” toward becoming procurement requirements.
Governance Features Were a Central Focus
One of the strongest themes throughout the workshop was operational governance.
Organizations are not only asking whether AI is secure, but whether it can be managed at scale.
The roadmap Ashwini shared during the session included extensive governance capabilities around Rovo access controls, agent permissions, connector restrictions, confidential data protection, and large-scale agent management.
Attendees showed particular interest in:
controlling who can create and deploy AI agents,
managing “agent sprawl” across large enterprises,
restricting sensitive connector content,
defining ingestion policies, and
introducing bulk management APIs for administration at scale.
Ashwini also previewed Guard-related capabilities focused on confidential data prompt controls, including regex and keyword-based protections designed to prevent sensitive information from being exposed through prompts or responses.
Future roadmap items included classification-based access controls, automated data classification, and data exfiltration protections.
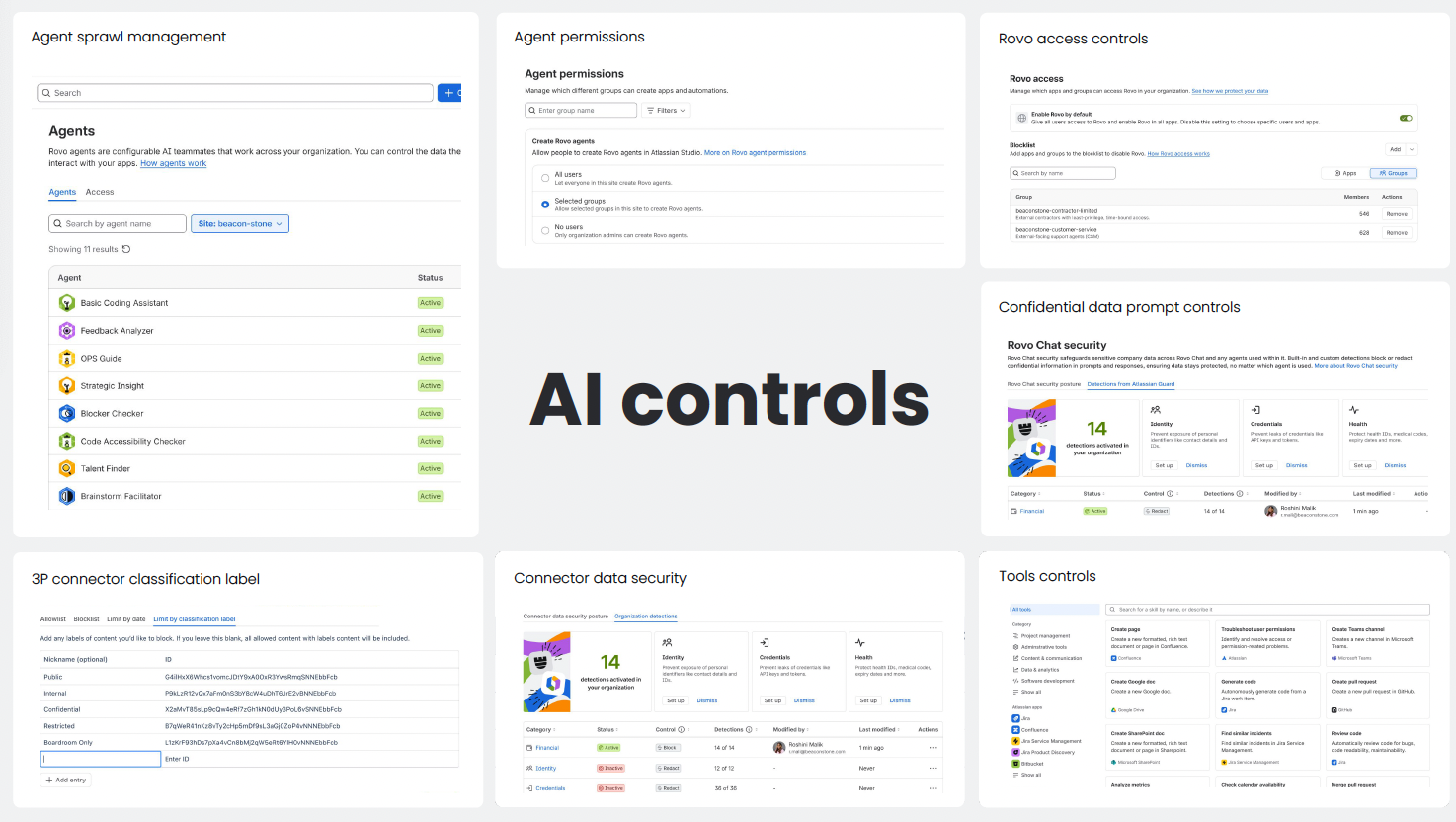
For regulated industries, these operational controls may ultimately matter just as much as the underlying AI models themselves.
Visibility, Auditability, and AI Insights
Another recurring request from customers is visibility – organizations want to understand not only who is using AI, but how it is being used, what it costs, and where risks may emerge.
Ashwini shared upcoming capabilities around audit logging, usage monitoring, and AI insights dashboards.
The roadmap includes:
agent invocation auditing,
visibility into external data access,
usage analytics and forecasting,
monitoring of AI credit consumption,
and reporting on blocked prompts and policy effectiveness.
Several attendees expressed concern about uncertainty around future pricing models and the risk of unexpected usage spikes. Some organizations had already encountered scenarios where experimental agent automations consumed credits far faster than anticipated.
Ashwini clarified that many common in-product AI features currently do not consume credits, while Rovo chat and agents do. Usage limits are visible today, though enforcement mechanisms are not yet active.
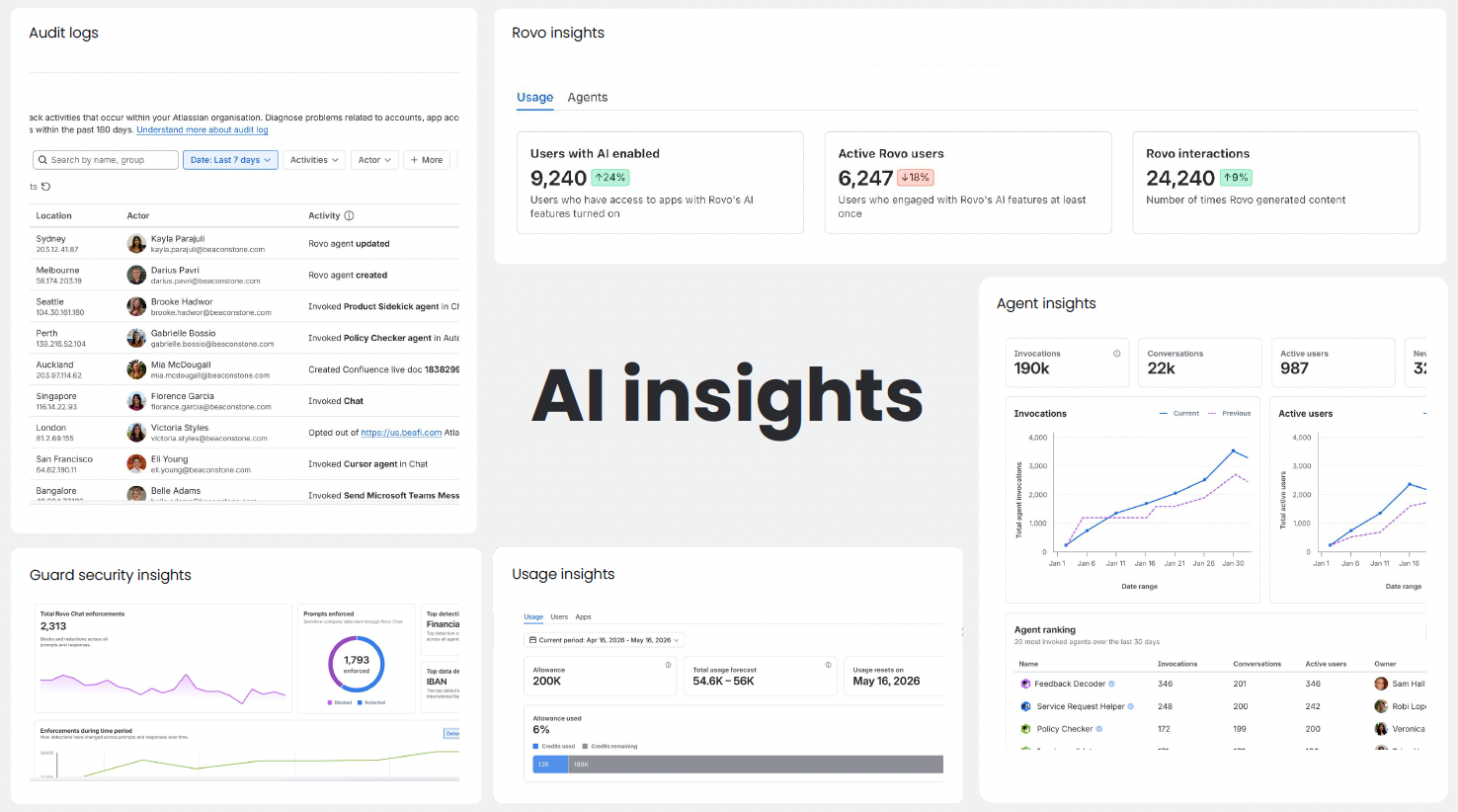
Even so, customers clearly want stronger predictability before enabling AI broadly across enterprise workflows.
One Theme Dominated the Entire Discussion: Trust
Perhaps the most interesting aspect of the workshop was that the conversation rarely focused on AI capability alone.
Instead, nearly every discussion returned to trust.
Trust in how data moves.
Trust in permissions.
Trust in governance.
Trust in transparency, including pricing transparency.
Trust in predictable operational behaviour.
The roadmap presented by Ashwini shows clear recognition that enterprise AI adoption in regulated industries will depend less on raw model power and more on governance maturity.
For organizations operating in regulated environments, AI adoption is no longer simply about innovation speed. It is increasingly about proving that innovation can happen safely, transparently, and with operational control.
For more on Rovo trust, please check out Atlassian’s dedicated AI Trust Center: AI Trust | Atlassian
Atlassian Government Cloud: Where Enterprise Cloud Meets Public Sector Requirements
The second major discussion during our Compliance Workshop at Atlassian Team26 focused on Atlassian Government Cloud (AGC) and the growing demand for cloud platforms capable of meeting government-grade security and sovereignty expectations.
Arjuna Rivera from Atlassian Government Cloud team took to the stage and told the audience where Atlassian Government Cloud stands today, what capabilities are already available, and where the roadmap is heading next.
As AI, compliance, and digital transformation continue accelerating across the public sector, one message became increasingly clear throughout the conversation:
Government organizations want modern cloud collaboration platforms but only if they can meet strict regulatory, operational, and sovereignty requirements.
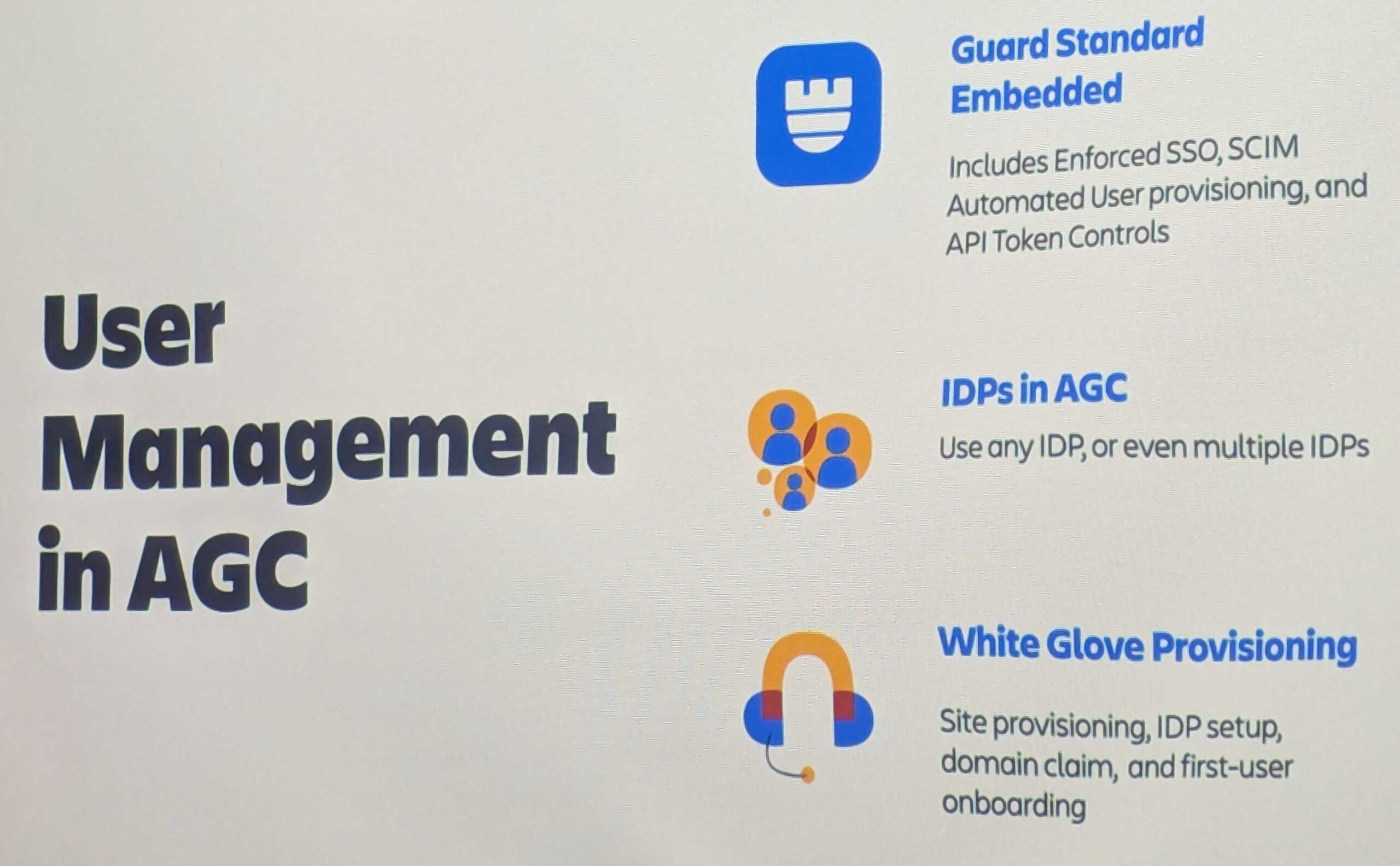
A Separate Environment Designed for Government Use
One of the most important clarifications during the discussion was that Atlassian Government Cloud is not simply a compliance layer added onto standard Atlassian Cloud.
AGC operates as a separate US-only environment running in AWS GovCloud regions on the US East and West coasts. It currently supports Jira, Jira Service Management, and Confluence, and includes its own dedicated AGC Marketplace ecosystem.

The platform has already achieved FedRAMP Moderate Authorization to Operate (ATO), positioning it as a viable option for many US federal agencies and regulated public sector organizations.
Access to AGC is intentionally restricted – the environment is currently limited to US government entities and approved supporting partners, reinforcing the separation between commercial and government workloads.
The discussion also highlighted that Atlassian Guard Standard is included by default, while support for multiple identity providers and domain claims is already available. Provisioning and identity management capabilities, however, are still evolving and were acknowledged as an active area of maturity.
Feature Parity with Commercial Cloud Is Still Evolving
A recurring theme throughout the conversation was feature parity – whether choosing AGC means sacrificing innovation speed compared to commercial Atlassian Cloud.
The answer today is: partially, but the gap is narrowing.
Confluence Live Docs are already available in AGC, while capabilities such as whiteboards and databases are not yet supported but are targeted for upcoming quarters.
Rovo also generated strong interest during this session. Arjuna confirmed that Rovo is not yet available within AGC environments, though it is firmly on the roadmap.
API parity follows a similar pattern – many APIs are already supported, but some remain unavailable where underlying product functionality has not yet reached AGC.
What stood out from the discussion was that Atlassian’s goal is not to create a permanently restricted version of Cloud, but to bring Commercial Cloud capabilities into a more secure environment built for government and highly regulated customers.

Jira Service Management Has Some Important Constraints Today
The conversation became particularly practical when discussing Jira Service Management within AGC.
One notable limitation today is that external customers cannot independently join JSM portals in the same way they can in commercial cloud environments. Instead, organizations currently need to provision users through their identity provider infrastructure.
Arjuna indicated this is expected to change later this year, which would significantly simplify external collaboration scenarios for agencies and contractors.
The session also confirmed that Assets functionality is already supported, while Statuspage has not yet arrived in AGC.
These kinds of operational nuances sparked a broader discussion around what “cloud maturity” really means for government organizations. In many cases, seemingly small collaboration features can have major workflow implications in highly regulated operational environments.
Next Big Milestones: FedRAMP High and DoD IL5
While FedRAMP Moderate is already in place, much of the audience interest centered on what comes next. Arjuna shared that both FedRAMP High and DoD IL5 are active targets for the platform roadmap.
This is particularly significant because those standards open the door to more sensitive government workloads, including defence-related use cases and organizations with stricter export control or ITAR requirements.
The roadmap discussions also referenced additional operational safeguards, including US-persons-only support models and tighter isolation boundaries expected within GovCloud environments.
For many attendees, these future certifications are likely to determine whether AGC becomes suitable only for selected workloads or capable of supporting entire regulated ecosystems.
Migration Paths Are Expanding
Organizations already invested in Atlassian Data Center or commercial Cloud want realistic pathways into AGC without major disruption.
Arjuna confirmed that migration support currently exists for:
Data Center to AGC,
Commercial Cloud to AGC for Jira and Confluence, and
ongoing work for Jira Service Management migrations.
A Cloud-to-Cloud Early Access Program was also mentioned as part of the broader migration evolution.
Many public sector organizations are now facing long-term infrastructure decisions around modernization, hosting strategy, and operational compliance. Clear migration pathways reduce friction for organizations considering transitions into more regulated cloud environments.
Sovereignty and Isolation Are Becoming Strategic Requirements
Beyond FedRAMP itself, one of the most interesting parts of the discussion focused on sovereignty.
The US government cloud roadmap appears relatively well-defined, but questions around European sovereignty requirements remain much more open. Arjuna acknowledged active discussions with European government stakeholders, though concrete details are still emerging.
The session also touched on Atlassian Isolated Cloud, which is expected to enter early access in the US this summer. Atlassian Isolated Cloud is a highly isolated single-tenant cloud environment with stricter ingress and egress controls, designed for extremely large or highly regulated customers.
Many organizations increasingly ask for isolation and sovereignty guarantees, but still want the operational simplicity of cloud delivery models. Isolated Cloud is intended to address that middle ground although with significantly higher cost expectations than standard cloud offerings.
Cost, Scale, and Enterprise Expectations
Licensing discussions reinforced that AGC is primarily targeted at larger organizations rather than smaller teams experimenting with government workloads.
Indicative minimums discussed during the session included:
200-user minimums for Jira and Confluence,
50-user minimums for Jira Service Management,
and pricing expectations roughly aligned with Enterprise licensing plus an additional uplift.
At the same time, Arjuna acknowledged that exceptions and negotiated arrangements may still exist through enterprise sales channels.
The pricing conversation reinforced a broader reality: government-grade cloud environments require additional operational, compliance and isolation investments, and those costs inevitably shape how these offerings are positioned.
The Bigger Picture: Government Cloud Is Becoming a Strategic Platform Decision
Perhaps the most interesting takeaway from the AGC discussion was that organizations are no longer evaluating government cloud purely through a compliance lens.
Today, agencies and regulated organizations are increasingly asking whether modern collaboration, AI, automation, and service management capabilities can coexist with sovereignty, security, and operational control requirements.
Atlassian’s approach suggests the company sees government cloud not as a niche deployment option, but as a long-term strategic platform direction.
And while there are still feature gaps, roadmap questions, and regional uncertainties to resolve, the overall direction presented at the Compliance Workshop showed a clear effort to bring modern cloud capabilities into some of the world’s most tightly regulated environments without forcing organizations to choose between innovation and compliance.
Check out the AGC platform and the apps that are already on AGC: apps for Atlassian products | Atlassian Marketplace
How Enterprise Security Expectations Are Reshaping the Atlassian Marketplace
The final session of the Compliance Workshop at Atlassian Team26 shifted the focus from Atlassian’s own platform capabilities to a rapidly growing challenge across the ecosystem:
How can enterprise customers trust the Marketplace apps they depend on?
Led by Sean Bourke and Phil Grove, the discussion explored how security, compliance, and procurement expectations are evolving for Atlassian Marketplace Partners – especially as larger regulated organizations continue moving critical workloads into Jira and Confluence Cloud.
One message was increasingly obvious throughout this session:
Enterprise app trust is no longer a “nice-to-have” differentiator. It is becoming a core purchasing requirement.
The Marketplace Trust Model Is Undergoing a Major Shift
One of the most significant announcements was that the current Cloud Fortified badge will be retired at the end of 2026.
In its place, Atlassian is preparing a new Marketplace trust program scheduled to launch in October 2026 with substantially higher expectations for vendors.
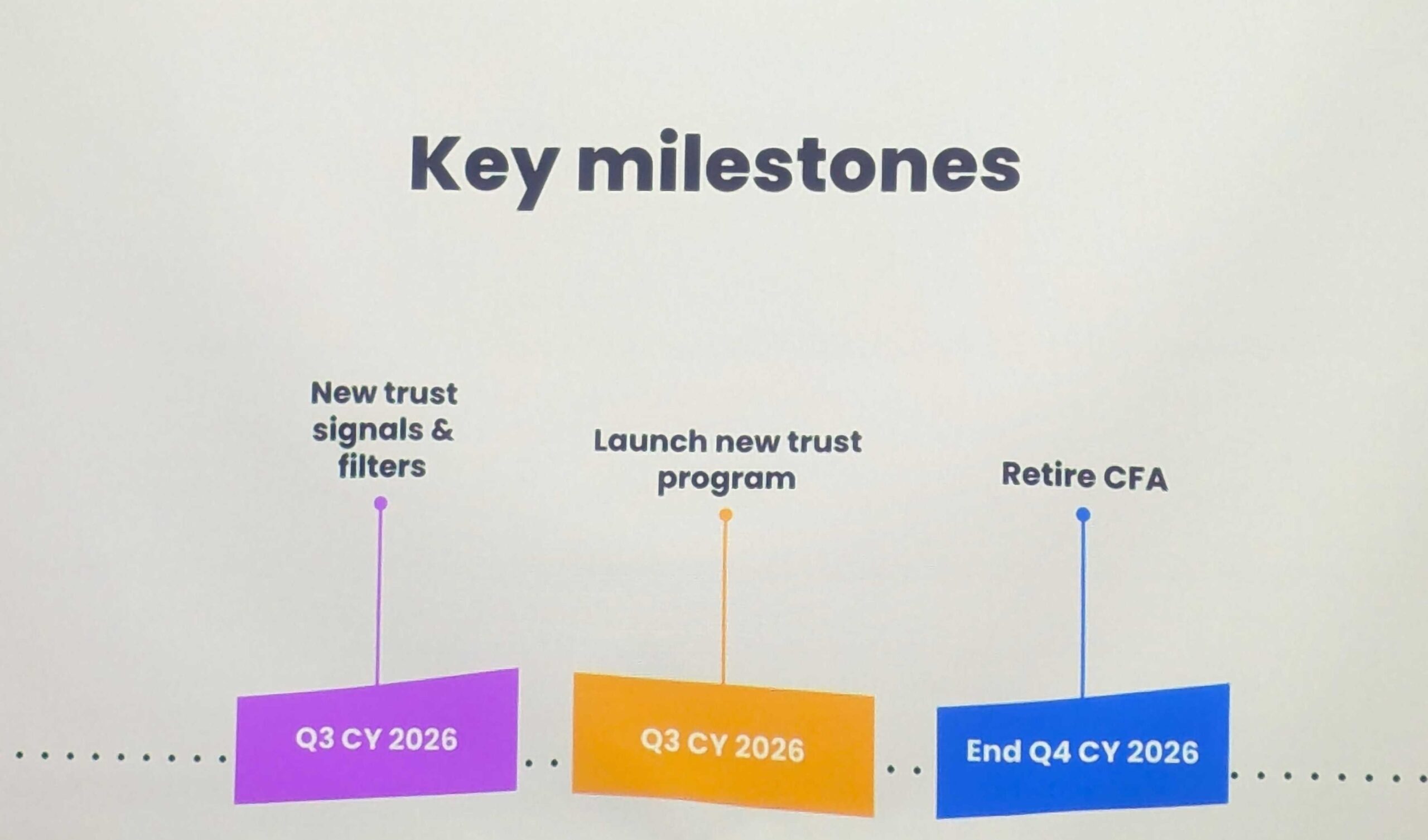
The discussion made it clear that the ecosystem is moving beyond lightweight trust indicators toward much deeper operational and security validation.
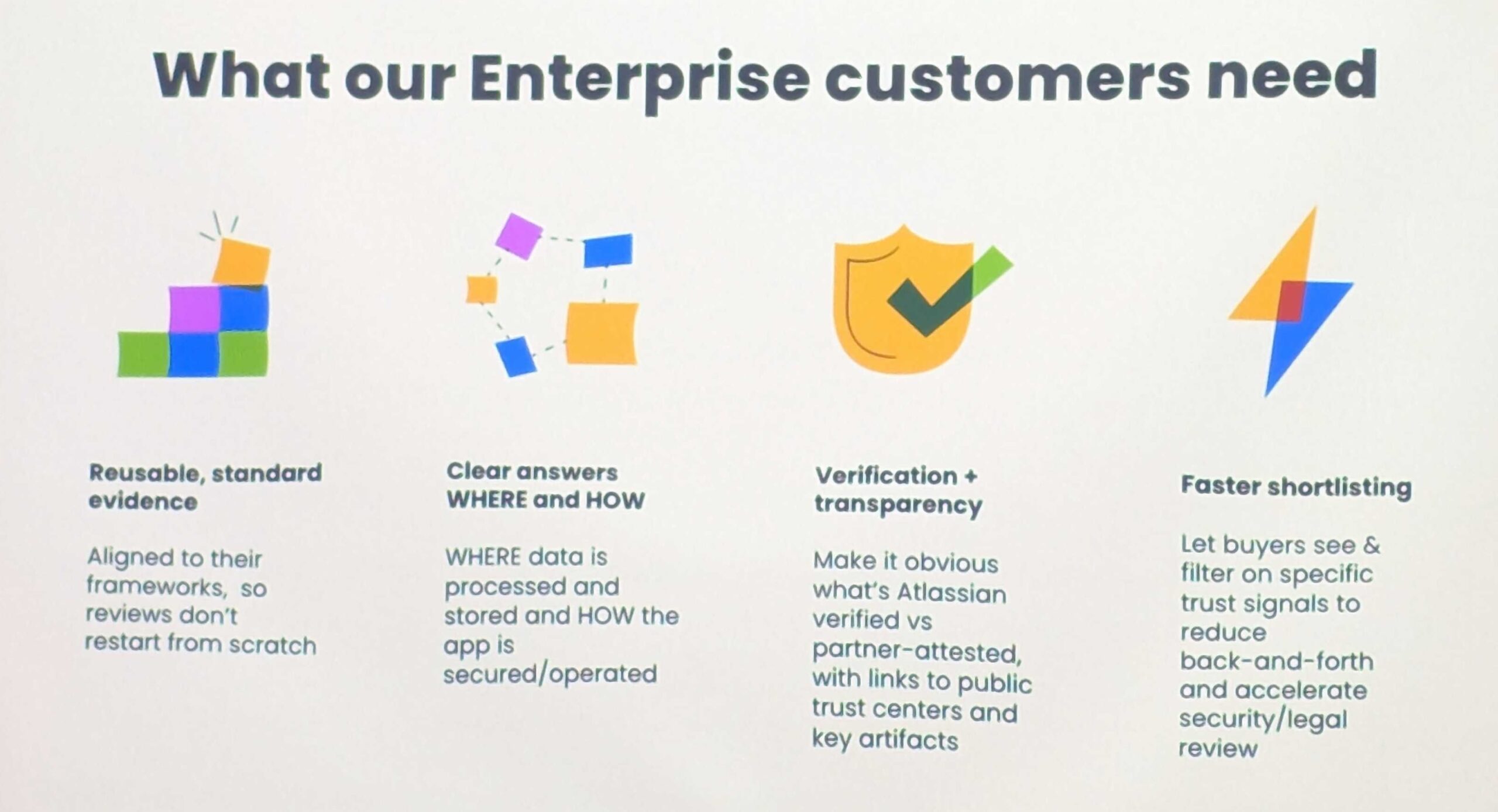
Historically, many app evaluations focused heavily on functionality and integration fit. Increasingly, however, enterprise buyers are scrutinizing operational controls, security posture, data handling practices, and compliance maturity before approving apps for production use.
The upcoming trust framework is designed to reflect that new reality.
Enterprise Procurement Has Become a Security Exercise
A particularly revealing part of the session focused on the operational burden enterprise customers now face during app procurement.
According to the discussion, many organizations are spending a huge amount of money internally just to evaluate and approve a single Marketplace app. That cost is not driven by licensing alone.
Instead, it reflects extensive security reviews, legal reviews, vendor assessments, compliance validation, procurement workflows, and risk management processes that increasingly surround third-party software adoption in regulated environments.
For Marketplace partners, this changes the conversation entirely. Trust signals are no longer simply marketing assets. They directly influence procurement friction, approval timelines, and purchasing decisions.
Customer-Controlled Egress Is Emerging as a Major Requirement
One of the most technically important topics discussed was customer-managed egress, currently in Early Access Program (EAP).
This capability is designed to give customers more granular control over how Marketplace apps communicate externally.
That matters because one of the largest concerns regulated organizations have with SaaS extensions is visibility into where data leaves the Atlassian platform and how external communications occur.
The direction Atlassian is taking suggests a future where organizations can apply much tighter governance around app-level network behaviour and external data flows.
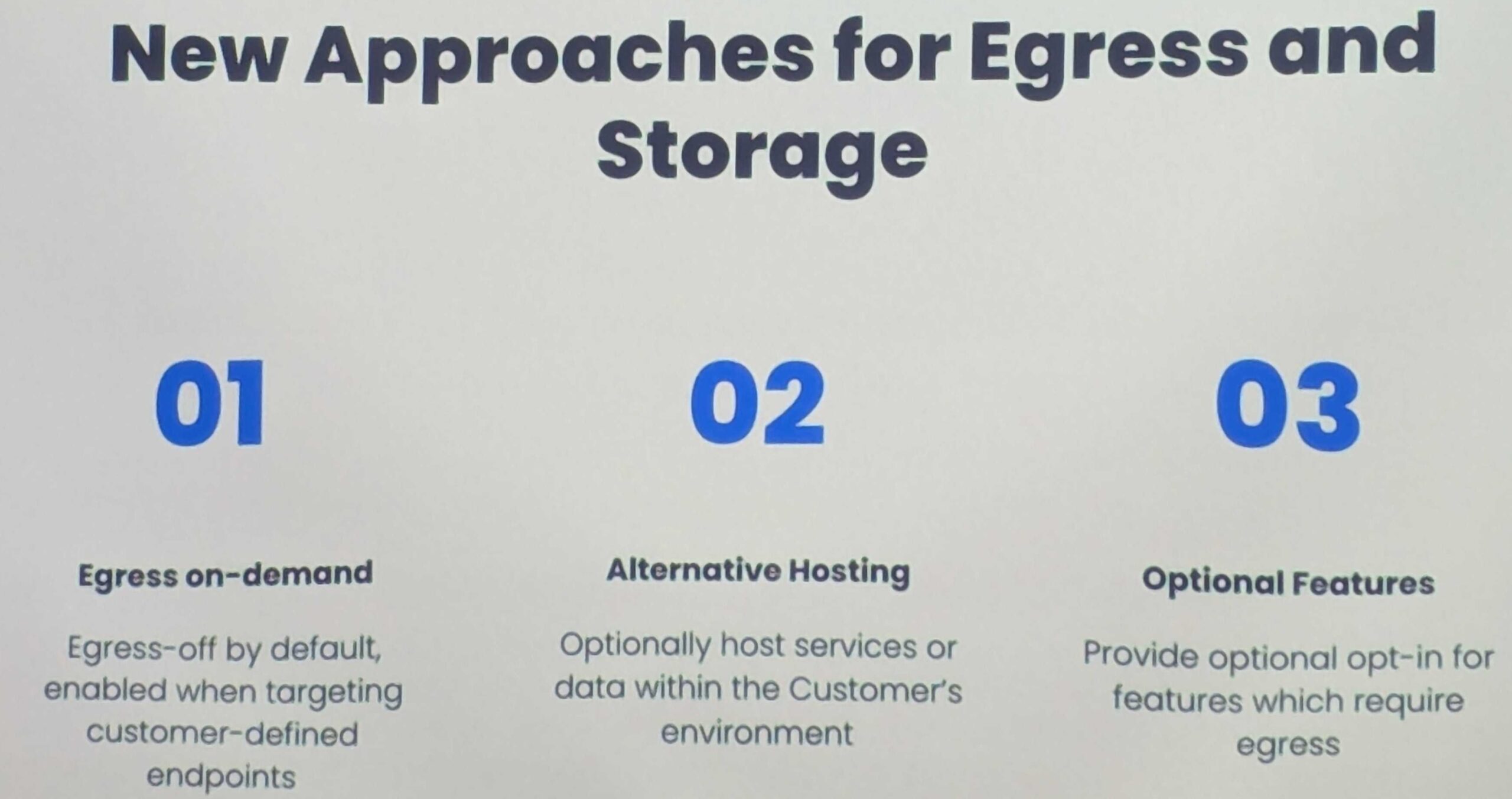
For enterprise security teams, this type of control is increasingly becoming mandatory rather than optional.
App Trust Signals Are Becoming More Transparent and More Searchable
Another important evolution discussed during the session was the increasing visibility of Marketplace trust indicators.
Customers will be able to filter and evaluate Marketplace apps based on criteria such as:
compliance certifications,
data residency capabilities,
participation in security programs, and
broader trust-related attributes.
This may sound like a small Marketplace UX improvement, but strategically it is much larger than that.
It effectively transforms security and compliance maturity into a competitive discovery factor within the Marketplace itself.
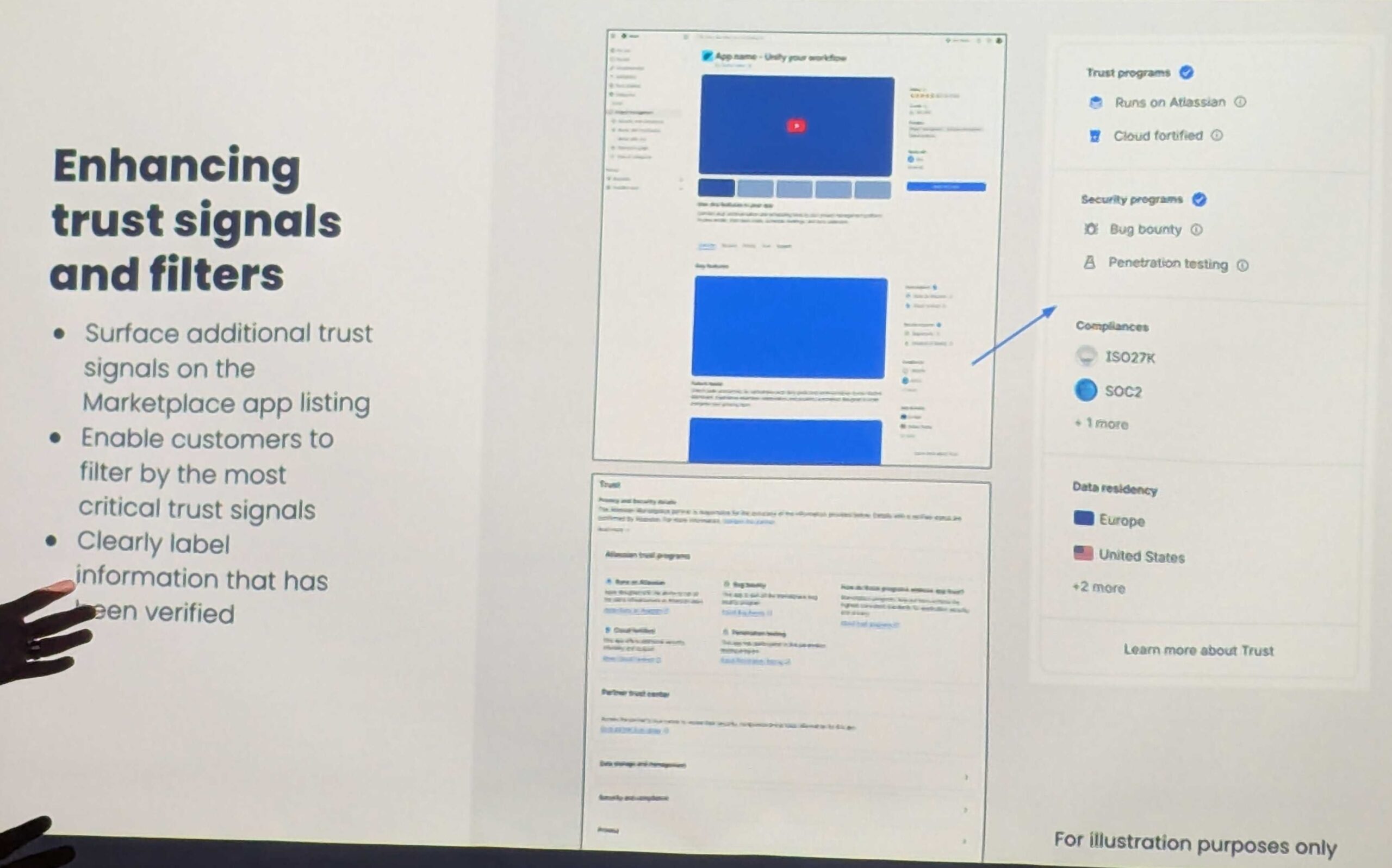
As enterprise adoption accelerates, organizations want faster ways to identify apps and vendors that already align with their governance expectations before beginning lengthy procurement reviews.
The Marketplace is gradually evolving from an app catalogue into a more enterprise-oriented trust ecosystem.
AI Governance Feedback Is Influencing the Roadmap
The discussion also connected directly back to earlier workshop conversations around Rovo and AI governance.
Phil emphasized that partner feedback is actively shaping ongoing roadmap decisions around regional AI boundaries, governance priorities, and enterprise controls.
This reflects a broader shift happening across the ecosystem. Customers are no longer asking only whether AI capabilities exist. They are asking where data is processed, how permissions are enforced, how AI actions are audited, and what controls administrators retain over autonomous functionality.
Marketplace partners are increasingly expected to align with those same governance expectations.
For more on Marketplace app Trust, visit Marketplace app Trust Program: https://www.atlassian.com/trust/marketplace
A Common Thread of the Workshop: Trust at Scale
Interestingly, all three workshop sessions: Rovo, Government Cloud, and Marketplace security, ultimately converged around the same core idea:
Trust has become the defining requirement for enterprise cloud adoption.
Whether discussing AI governance, sovereign cloud environments, or Marketplace applications, the underlying customer questions were remarkably similar:
Can we control it?
Can we audit it?
Can we govern it?
Can we trust it at scale?
The conversations at the Compliance Workshop in Team26 suggested that Atlassian and its ecosystem partners increasingly recognize that enterprise growth in regulated industries will depend not only on delivering innovation quickly, but on proving that innovation can operate safely inside some of the world’s most demanding environments.
If you’re an Atlassian partner or customer grappling with these issues and would like to learn more about what our workshop uncovered, reach out to us and we will be happy to schedule some time to discuss further.





